Coding Practice: Day 2
Discovered information disclosure via buffer over-read vulnerability
What is a buffer over-read vulnerability?
This is when a program with undefined behavior reads more than the intended memory from a buffer.
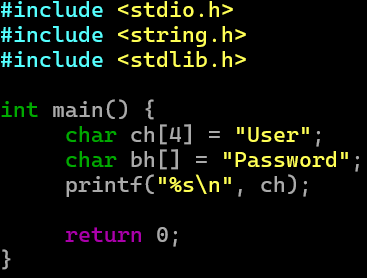
For example, initializing a char array with 1 less byte of memory than it needs leaves out the null terminator ‘\0’ which means printing that char array will print the next strings in memory until there is a null terminator.
You can see in the program here, I create several char arrays like User, password1, password 2, etc… and none of them have been initialized with enough space for the null terminator. Like for example, the string “User” should have 5 characters: “User\0’ where ‘\0’ is one character, the null terminator.
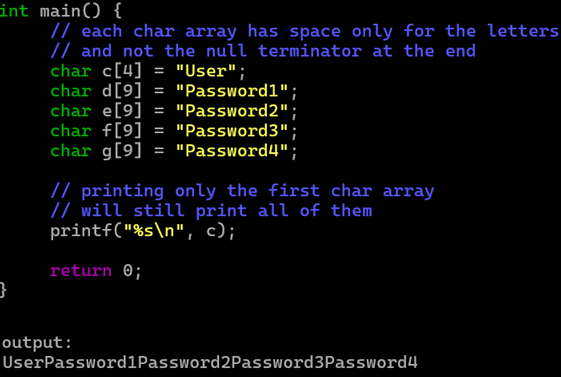
We print with printf and insert only the first char array “User”, but it prints all of the passwords as you can see in the output. This is because there is no null terminator telling the program to stop reading.
Thus allowing us to see all the password char arrays. Of course, this would probably never happen in modern code, but if memory isn’t allocated properly like this, a program can overread any hardcoded secrets or keys.
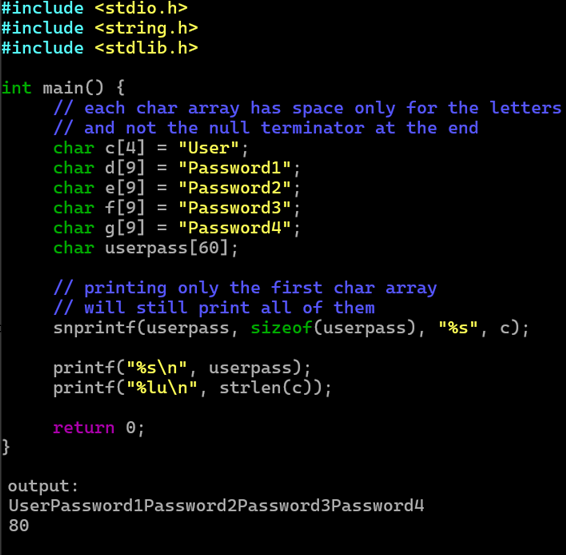
Also, any C functions that don’t stop reading until hitting a null terminator will behave the same away. Here we see snprintf() taking just the char array c which stores the string “User”, but it still prints the remaining char array passwords.
strlen() behaves the same way, counting the bytes in a char array until hitting a null terminator, which is why it counts the bytes in all the char array passwords here.
On top of this vulnerability, the compiler, GCC (and I don’t know if any other programs war) doesn’t even warn about it, which is why if specifying the allocated size when initializing a char array, make sure it has the correct amount of memory, or just use dynamic memory allocation with ‘char arr[]’.
I did notice that when compiling with GCC, if you do an optimization of level 1 and 2 (via the -O1 and -O2 flags), the program memory is arranged in a way that causes the program to not do a buffer over-read. Meaning, the output is just:
User
8
I also noticed using clang to compile the programming produced the output:
User
4
This is getting into compilers and how they behave which I will look into later.
I tried using cppcheck as well to see if it could spot the buffer over-read vulnerability. It didn’t detect the root cause, but it detected that strlen() needed to a null terminator to work properly.
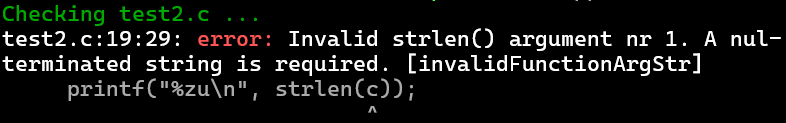
From there, we could try to trace back to the root cause of the problem.
‘strlen()’ still works properly in the program, but because of the undefined behavior of initializing the char array with no space for the null terminator, it works in an unintended way.
If anyone is reading this, please let me know if you actually found this helpful, so I know whether to keep these as writeups for myself or detailed explanations.
